nxtractor: My Simple Data Recovery Application for Linux
Want to recover files? For a proper Open Source data recovery software, see CGSecurity’s TestDisk and PhotoRec.
Once upon a time I had no stable internet connection, mult.ru distributed their “Масяня” movies as .exe files and I was not happy with them on the linux system.
In order to make a standalone movie, flashplayer.exe was simply concatenated with .SWF file, so to get .SWF file I simply needed the offsets and end markers (if any).
I wrote a simple application in C that was doing exactly this.
At some point in time my friend Alex asked me to see whether it is possible to recover any data from his hard drive which had the file system table completely overwritten by something and no data recovery software was able to extract anything.
I dumped the image of the whole 20Gb drive and began thinking about the way the data can be recovered if we don’t know where to look.
And so the nxtractor project was born. During next couple of days I was examining the signatures and markers of the most common file types, wrote the scanner that was sufficiently good and extensible.
I did not recover much information from that drive, the data was too fragmented.
This was back in 2003.
Fast forward to today, when SD cards hold the same amount of data as the hard drives of the past, data storage devices are used by music players, phones and cameras.
Now imagine you have deleted all the photos from the camera. What would you do?
sudo dd if=/dev/mmcblk0p1 of=~/mmcblk0p1.bin bzr branch lp:~rye/+junk/nxtractor cd nxtractor make ./nxtractor ~/mmcblk0p1.bin
Yes, that’s the ideal variant, in some cases you will need to do adjustments to the types.dat file, for example to prevent false positives on TIFF files you comment out the whole type=tiff block. To make sure you are not extracting embedded data in JPEG files, set minsize in type=jpeg to 1000000 which means that it will not consider files that are less than 1Mb to be real jpeg files.
For example, my recent removal of the photos resulted in the following:
nxtractor ~/mmcblk0p1.bin Scanning started at Sun Mar 18 13:34:01 2012 @365056: Found magic numbers for jpeg. Size: 1043563 @1413632: Found magic numbers for jpeg. Size: 1249863 @2691584: Found magic numbers for jpeg. Size: 1225140 @3936768: Found magic numbers for jpeg. Size: 726782 @4690432: Found magic numbers for jpeg. Size: 685591 @5378560: Found magic numbers for jpeg. Size: 860730 @6263296: Found magic numbers for jpeg. Size: 712114 @6984192: Found magic numbers for jpeg. Size: 757930 @7770624: Found magic numbers for jpeg. Size: 872590 ... @59707904: Found magic numbers for jpeg. Size: 1775034 Scanning finished at Sun Mar 18 13:34:05 2012 Extraction started at Sun Mar 18 13:34:05 2012 Writing mmcblk0p1.bin.nx/jpeg/365056.jpg (1043563 bytes) ... Writing mmcblk0p1.bin.nx/jpeg/59707904.jpg (1775034 bytes) Extraction finished at Sun Mar 18 13:34:05 2012
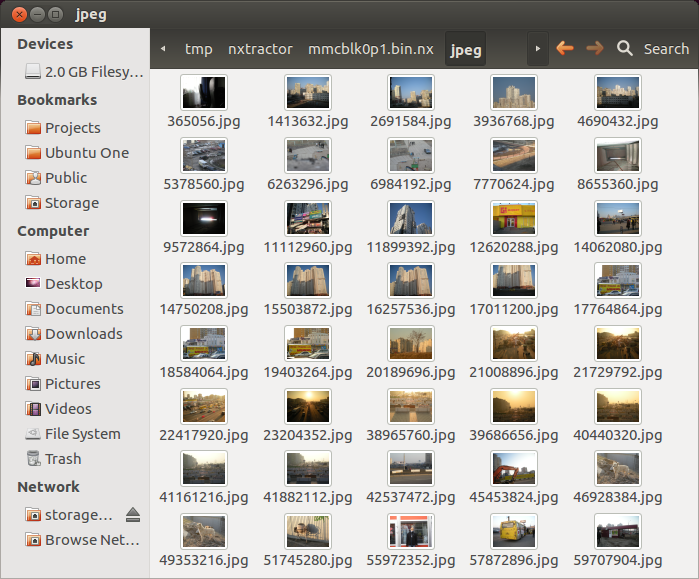
And I got my files back! Several years after I wrote the software. It’s amazing :)
This software is provided AS IS and I have no plans developing it any more, use at your own risk…
And please, backup your sensitive data. NOW.