Warning: Samsung ChatON
Update (2012-12-04): I have installed the client again and tried to intercept messages. It looks like the server-side was fixed and now every server uses encryption (likely AES) to encrypt the protobuf payload. The key for the payload is negotiated over HTTPS connection. So it is moderately safe to use ChatON on the public networks. However, file uploads and downloads are still using plain HTTP connection and that means they can be easily intercepted.
There is also an online version of ChatON which uses HTTPS only and a different set of servers.
This is a final update. I will most likely not use ChatON in the future unless I replace my phone as the recommended Android version is 2.3 (I have 2.2). Samsung does provide access to the Server API http://developer.samsung.com/chaton-api, but it is currently in closed beta, so no protocol details are shared.
Old content goes below:

tl;dr version: Do not use ChatON on the public WiFi networks. The communication between client and server is not encrypted.
Two days ago Samsung launched their new IM service ChatON. ChatON Android application was released and its UI is definitely awesome. Having obtained my copy from Android Market I decided to check what protocol it is using for communication.
I launched tcpdump on my (rooted) Acer Liquid and started listening for the messages.
Among the lines of https (encrypted) messages flowing back and forth I found the following:
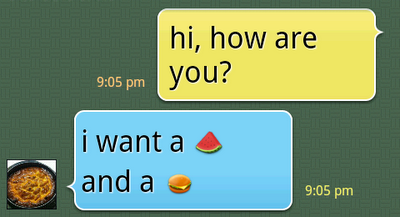
21:05:01.146225 IP 46.203.98.114.42914 > 46.137.191.242.5223: P 118:345(227) ack 1 win 5600 0x0000: 4500 0117 30e8 4000 4006 8940 2ecb 6272 E...0�@.@..@.�br 0x0010: 2e89 bff2 a7a2 1467 ab45 ae43 4473 fdf8 ..����.g�E�CDs� 0x0020: 8018 15e0 fab9 0000 0101 080a 00db c787 ...���.......��. 0x0030: 0ba8 7d12 6264 3530 6263 3337 2d65 6532 .�}.ba50bc37-ee2 0x0040: 382d 3432 6366 2d61 6531 352d 3133 3731 8-42cf-ae15-1371 0x0050: 3334 3466 3363 3464 0104 00bb 08cd f7ef 344f3c4d...�.�� 0x0060: 87d8 e820 1000 1800 2248 3462 3064 6365 .��....."H4b0dce 0x0070: 6638 2d64 3733 322d 3464 3038 2d62 3062 f8-d732-4d08-b0b 0x0080: 612d 6536 3862 3263 3931 3066 6662 6264 a-e68b2c910ffbbd 0x0090: 3530 6263 3337 2d65 6532 382d 3432 6366 50bc37-ee28-42cf 0x00a0: 2d61 6531 352d 3133 3731 3334 3466 3363 -ae15-1371344f3c 0x00b0: 3464 2a0c 3338 3039 3133 3532 3930 3539 4d*.380913529059 0x00c0: 320c 3338 3039 3337 3532 3539 3836 3a24 2.380937525986:$ 0x00d0: 6264 3530 6263 3337 2d65 6532 382d 3432 bd50bc37-ee28-42 0x00e0: 6366 2d61 6531 352d 3133 3731 3334 3466 cf-ae15-1371344f 0x00f0: 3363 3464 420f 3335 3335 3039 3033 3132 3c4dB.3535090312 0x0100: 3536 3238 354a 1068 692c 2068 6f77 2061 56285J.hi,.how.a 0x0110: 7265 2079 6f75 3f re.you? 21:05:07.236157 IP 46.137.191.242.5223 > 46.203.98.114.42914: P 228:422(194) ack 345 win 62 0x0000: 4500 00f6 af74 4000 3206 18d5 2e89 bff2 E..��t@.2..�..� 0x0010: 2ecb 6272 1467 a7a2 4473 fedb ab45 af26 .�br.g��Ds�۫E�& 0x0020: 8018 003e b6d2 0000 0101 080a 0ba8 8550 ...>��.......�.P 0x0030: 00db c787 6264 3530 6263 3337 2d65 6532 .��.ba50bc37-ee2 0x0040: 382d 3432 6366 2d61 6531 352d 3133 3731 8-42cf-ae15-1371 0x0050: 3334 3466 3363 3464 0106 009a 0a48 3462 344f3c4d.....H4b 0x0060: 3064 6365 6638 2d64 3733 322d 3464 3038 0dcef8-d732-4d08 0x0070: 2d62 3062 612d 6536 3862 3263 3931 3066 -b0ba-e68b2c910f 0x0080: 6662 6264 3530 6263 3337 2d65 6532 382d fbbd50bc37-ee28- 0x0090: 3432 6366 2d61 6531 352d 3133 3731 3334 42cf-ae15-137134 0x00a0: 3466 3363 3464 1000 1a4a 0a0c 3338 3039 4f3c4d...J..3809 0x00b0: 3337 3532 3539 3836 120c 3338 3039 3133 37525986..380913 0x00c0: 3532 3930 3539 1884 d185 fb9e c816 221b 529059..�.�.�.". 0x00d0: 6920 7761 6e74 2061 205b 686d 5d20 616e i.want.a.[hm].an 0x00e0: 6420 6120 5b35 286c 6c29 5d28 c3e5 bb98 d.a.[5(ll)](���. 0x00f0: b126 3000 2800 �&0.(.
Do you see something?
Here’s what you saw:
Basically, connection to the server is not (always) encrypted.
The client is using Google Protobuf protocol to send messages back and forth between client and server and the communication is not encrypted in any way. After more careful examination I found that the session initiation IS encrypted, so that it may not be possible to find whom exactly with you are talking to but all the messages will be visible to everybody around you if you are using an unencrypted open network such as you can find at the local cafe shops, restaurants, shopping centres etc.
You may not be in that amount of danger if you are using your cell phone carrier for the internet connection, that communication is encrypted between your phone and the cell towers, however you might not always realize that you have switched to open WiFi network and keep using ChatON.
I don’t have a Bada-powered device nearby to verify whether that uses the same servers so I will assume that the same unencrypted protocol is used on all Bada devices and Samsung featurephones that have ChatON installed unless I have the proof that it is doing otherwise.
Interesting geeky detail – the servers are running on port 5223 which is usually associated with XMPP over SSL but it is actually a proprietary protocol (well, based on Google’s protobuf). The chat servers are running on Amazon AWS hosts.
File uploads are also running over plain HTTP/1.1 without encryption:
POST /file?uid=bd50bc37-...-1371344f3c4d¶m=7daffaa462b802b...92e37870 HTTP/1.1 content-type: image/jpeg content-length: 48401 User-Agent: Dalvik/1.2.0 (Linux; U; Android 2.2.2; Liquid Build/FRG83G) Host: eu.file.samsungchaton.com Connection: Keep-Alive ... GET /4b/0d/ce/f8/d7/32/4d/08/b0/ba/e6/8b/2c/91/0f/fb/4b0dcef8-d732-4d08-b0ba-e68b2c910ffb/ 1318879486269_239.jpg?AWSAccessKeyId=AKIAIXENATYOW4T2DJSQ& Expires=1319052296&Signature=6UFD%2FYS9Vlls9X7WJov8GcH7EGs%3D HTTP/1.1 User-Agent: Dalvik/1.2.0 (Linux; U; Android 2.2.2; Liquid Build/FRG83G) Host: eu.chaton-file.s3.amazonaws.com Connection: Keep-Alive HTTP/1.1 200 OK x-amz-id-2: PNglgPsPAkR7SvhFPHk2bkl901Q6MGedePoaCRf/RGArSM36lZgtkMWLN10nmzZK x-amz-request-id: E25D27220B372F64 Date: Mon, 17 Oct 2011 19:24:58 GMT Last-Modified: Mon, 17 Oct 2011 19:24:51 GMT ETag: "3ec7437168455698b4367ed303bfcfad" Accept-Ranges: bytes Content-Type: image/jpeg Content-Length: 738 Server: AmazonS3 ...
Ah, when user is not properly registered (ChatON on Android Emulator) the message returned is…
13:56:58.562553 IP 46.203.53.202.59299 > 46.137.191.242.5223: P 216:450(234) ack 185 win 3456 0x0000: 4500 011e df2c 4000 4006 079d 2ecb 35ca E...�,@.@....�5 0x0010: 2e89 bff2 e7a3 1467 38a3 84e8 4513 9da9 ..����.g8�.�E..� 0x0020: 8018 0d80 2c9f 0000 0101 080a 001a 66c4 ....,.........f 0x0030: 0c05 21a6 6264 3530 6263 3337 2d65 6532 ..!�bd50bc37-ee2 0x0040: 382d 3432 6366 2d61 6531 352d 3133 3731 8-42cf-ae15-1371 0x0050: 3334 3466 3363 3464 0104 00c2 088a e2a2 344f3c4d...�.. 0x0060: fea5 8004 1000 1800 2248 6264 3530 6263 ��......"Hbd50bc 0x0070: 3337 2d65 6532 382d 3432 6366 2d61 6531 37-ee28-42cf-ae1 0x0080: 352d 3133 3731 3334 3466 3363 3464 6366 5-1371344f3c4dcf 0x0090: 6662 3933 3939 2d63 3935 332d 3462 6465 fb9399-c953-4bde 0x00a0: 2d39 3266 352d 6639 6435 3136 3862 3562 -92f5-f9d5168b5b 0x00b0: 3764 2a0c 3338 3039 3133 3532 3930 3539 7d*.380913529059 0x00c0: 320c 3338 3036 3336 3137 3038 3335 3a24 2.380636170835:$ 0x00d0: 6264 3530 6263 3337 2d65 6532 382d 3432 bd50bc37-ee28-42 0x00e0: 6366 2d61 6531 352d 3133 3731 3334 3466 cf-ae15-1371344f 0x00f0: 3363 3464 420f 3335 3335 3039 3033 3132 3c4dB.3535090312 0x0100: 3536 3238 354a 174e 6f77 2069 7420 6973 56285J.Now.it.is 0x0110: 2077 6f72 6b69 6e67 2061 6761 696e .working.again 13:56:59.643944 IP 46.137.191.242.5223 > 46.203.53.202.59299: P 185:369(184) ack 450 win 62 0x0000: 4500 00ec 8237 4000 3206 72c4 2e89 bff2 E..�.7@.2.r�..� 0x0010: 2ecb 35ca 1467 e7a3 4513 9da9 38a3 85d2 .�5�.g��E..�8�. 0x0020: 8018 003e a34b 0000 0101 080a 0c05 2a79 ...>�K........*y 0x0030: 001a 66c4 6264 3530 6263 3337 2d65 6532 ..f�bd50bc37-ee2 0x0040: 382d 3432 6366 2d61 6531 352d 3133 3731 8-42cf-ae15-1371 0x0050: 3334 3466 3363 3464 0105 0090 088a e2a2 344f3c4d...... 0x0060: fea5 8004 1248 6264 3530 6263 3337 2d65 ��...Hbd50bc37-e 0x0070: 6532 382d 3432 6366 2d61 6531 352d 3133 e28-42cf-ae15-13 0x0080: 3731 3334 3466 3363 3464 6366 6662 3933 71344f3c4dcffb93 0x0090: 3939 2d63 3935 332d 3462 6465 2d39 3266 99-c953-4bde-92f 0x00a0: 352d 6639 6435 3136 3862 3562 3764 1a13 5-f9d5168b5b7d.. 0x00b0: 0a0e 3436 2e31 3337 2e31 3137 2e32 3334 ..46.137.117.234 0x00c0: 10e7 2820 96cc b5b5 b126 2a20 08f2 2e12 .�(..̵��&*..�.. 0x00d0: 1b4d 6573 7361 6765 2052 6563 6569 7665 .Message.Receive 0x00e0: 7220 6973 2049 6e76 616c 6964 r.is.Invalid